Imperva Acquires CloudVector
The price was not revealed.
Israeli Cybersecurity company Imperva has revealed that it plans acquire application programming interface (API) security company CloudVector. The acquisition price has yet to be disclosed.
IBM explains that Application programming interfaces, or APIs, simplify software development and innovation by enabling applications to exchange data and functionality easily and securely. API enables companies to open up their applications’ data and functionality to external third-party developers, business partners, and internal departments within their companies. And nowadays this is almost always done using cloud services.
Shadow APIs are published by third parties and can be deployed outside of a process defined by the original application’s developer. The API owners are not always aware of the use of a shadow API and are ripe for exploitation by hackers.
There is a reason why there are so many cybersecurity startups today. Cybersecurity is more important than ever. Hackers are not only motivated by money or politics. They often just like being malicious. So even small companies need to be on their guard and be sure to properly protect their systems. And so do non-profit organizations and especially any and all government systems and servers.
And this is in addition to the innumerable number of everyday people out there who risk virus and malware infections every time that they turn on their home computers or use their cell phones.
–
[embedded content]
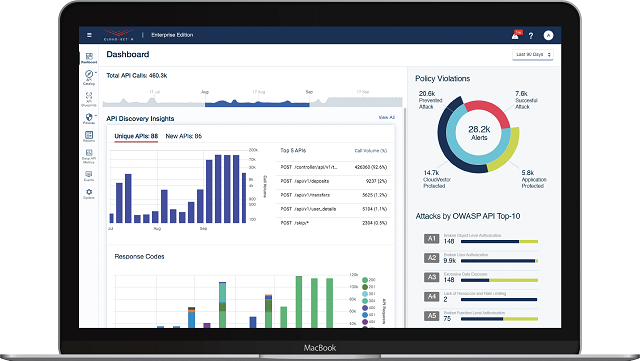
Founded in 2018, CloudVector is a provider of advanced API Threat Protection, enabling its customers to “discover, monitor, and secure all API data in any environment with Deep API Intelligence. CloudVector boasts that it provides the deepest visibility into API behavior, the broadest support for computing environments, and the lightest touch on DevOps. The company states that it leverages artificial intelligence and machine learning to automatically and continuously generate and catalog API analytics, which it monitors for anomalous behavior. CloudVector’s unique micro-sensor architecture is easily deployed into any environment with no changes to code. CloudVector states that it is eliminating an API security blind spot by protecting against the entire OWASP API Security Top 10.
Founded in 2002, Imperva calls itself a cybersecurity leader with a mission to protect data and all paths to it. The company states that it protects the data of over 6,000 global customers from cyber attacks through all stages of their digital transformation.”Our products are informed by the Imperva Research Lab, a global threat intelligence community, that feeds the latest security and compliance expertise into our solutions,” explains Imperva.
The company was acquired by Thoma Bravo for $2.1 billion in 2018. It has acquired other companies recently, including jSonar and Distil Networks, Tomium, Camouflage, and Prevoty.
–
NEWS: Imperva has entered an agreement to acquire CloudVector, a leader in advanced API security, that discovers, monitors and protects #API traffic in any environment from exploits and breaches. https://t.co/rVEglZU8yN pic.twitter.com/TtDnkY92fb
— Imperva (@Imperva) May 3, 2021
“As a pioneer in modern API security, Imperva protects our customers from the risks associated with the mis-use of APIs via exposures or attacks, and the exfiltration of sensitive data. Over the last year, we’ve seen significant acceleration in the number and volume of production APIs, such that API-related traffic now makes up more than 70% of our Cloud WAF traffic,” says Pam Murphy, CEO, Imperva. “Combined with an expanding surface area and novel exploits, all organizations need stronger API visibility and advanced protection. The addition of CloudVector fits perfectly with our vision, advances our API security solution, and most importantly, broadens the security of our customers’ applications and data.”
Steven Schoenfeld SVP Product Management of Imperva said in a blog post, “I am excited to announce Imperva has entered into an agreement to acquire CloudVector to advance our mission to protect data and all paths to it. Together, we believe we can change what organizations expect from Web Application and API Protection solutions. There are multiple reasons APIs are at the top of Imperva’s key investment areas, and they are all about the future of applications and the ways they are compromised.”
He explained that Shadow APIs are the new shadow IT, but riskier. Shadow APIs do not fade on their own, they expand. In today’s world, application development teams move quickly to respond to business needs. When APIs are published without security review and controls they present a risk in addition to their benefit. Probing attackers can use them to access your organization’s data. API discovery is a necessity for combatting this growing risk of shadow APIs.
Read more about: CloudVector, CyberSecurity, Imperva